Apple focusing on privacy is proving to be beneficial for customers. Unfortunately, the high cost of products deters many from owning a device. This brings into focus the price of online security. Is there a two-tier internet when it comes to privacy?
Internet consumer models
There are three distinct consumer facing internet business models; advertising, donation and pay.
- Facebook is the most recognisable free at the point of use Internet product. It derives the majority of its income from advertisers and its content from users.
- Donation models rely on users support through donating cash or personal time. Examples include online news sites, not-for-profit and charitable services.
- And there are straightforward payment models.
A few brands stick to a single business model; Wikipedia is the best known. Many of the most famous online brands run on a combination of these models. Google, as an example, combines subscription and advertising for its free service.
Apple model
Apple developed a different business approach. It built the company on quality hardware providing internet and downloadable services. Advertising forms a small percentage of its total revenue. The core income derives from selling computers. Charging App developers for access to the Apple ecosystem has also proved lucrative. Apple is one of the world’s most valuable companies, with dollar reserves in the billions.
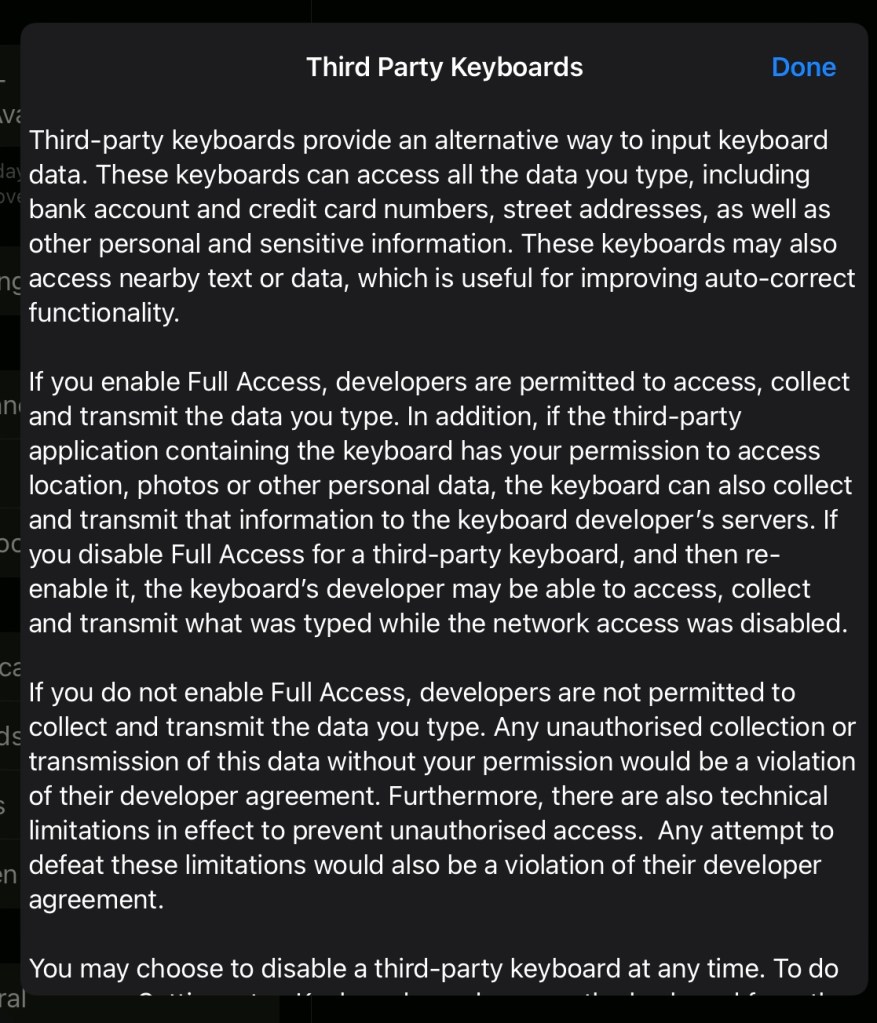
For its supporters, the success of the brand is about quality, both of the devices and security. Unlike the advertising model, Apple does not sell customer or user data. Privacy sits at the centre of the business model. For Apple loyalists, it’s the most important aspect of owning an Apple over another product.
Two-tier internet
An Apple laptop can be three or four times the cost of other laptops on the market. Those who cannot afford an Apple device can find security cumbersome. Protecting data involves purchasing security software. Enabling security requires a degree of understanding of the device settings. It can be a daunting task.
Creating and maintaining security settings is complex. To keep on top of all the threats is time-consuming. Ignoring security leaves users open to great peril. Risks like someone stealing bank login details is commonly understood. Longer-term risks are less appreciated. Companies build profiles on individuals over an extended period based on internet usage. Browsing habits, fitness data, travel apps and social media posts all provide aspects of a person’s profile. Over years, how much will this data determine the cost of medical care, insurance or where a person may live?
There is a real risk of commercial exploitation of data in the future. Unchecked, this will be much worse than anything being experienced at the time of writing.
There is also the reality of what a hostile government could do? Brexit has already shown the power of data manipulation (see Cambridge Analytica reports). Profiling could be used to curtail fundamental liberties in the future. This is already evident in some countries. [1]
Apple has long recognised these risks. In response, it is actively seeking to protect, at least in part, customers. But what about those who cannot afford Apple products? Who will be looking out for their privacy? Their protection?
Market solution
As it stands, the market is encouraged to protect people from these risks. Except the market tends to serve the wealthier at the expense of the most vulnerable.
Conclusion
The scale of Apple now allows it to dictate how all others within its ecosystem behaves. The company also has increased power outside of its ecosystem. The board of Apple recognised that customers were becoming concerned about privacy. Its response was to introduce a raft of measures to reduce app owners ability to harvest users data. Apple’s response needs to be replicated by governments and institutions. All citizens need the protections Apple is seeking to provide its customers. Data protection should be regardless of personal financial circumstances.
John M
[1] see Brexit Britain


Leave a comment